Almost every framework that touches your security or compliance program expects you to prove you have policies — not just write them once and forget. SOC 2 calls it out across CC1.4 (commitment to integrity & ethical values) and CC2.3 (the entity communicates information). ISO 27001:2022 lays it down in A.5.1 (policies for information security must be approved, communicated, and reviewed). FFIEC’s IT Booklet dedicates a whole section to policy ownership and review cadence. Auditors want to see the policy exists, who owns it, when it was last reviewed, and what the cadence will be going forward.
Most teams handle this with a SharePoint folder and a calendar reminder for the compliance lead. Renewals get missed. Owners turn over. The policy survives but the program around it doesn’t. Talarity treats every imported policy as a first-class artifact — the same primitive that runs your DR tests, attestation drives, and audit reports — so the whole lifecycle is visible in one place.
This article covers importing an existing policy (a PDF or DOCX you already have), setting an owner, configuring review reminders, and walking the cross-link between the Policies tab and the Artifact Repository. Authoring a policy from a template is a separate workflow — covered in another article.
Who’s involved
- Compliance lead — uploads the policy, picks the owner, sets the review cadence.
- Policy owner — typically the CISO, Privacy Officer, or HR Director. Gets the review-due reminders. On the hook for keeping the policy current.
- Auditor — pulls the policy + linked artifact + review history at audit time. Confirms the policy was reviewed within cadence.
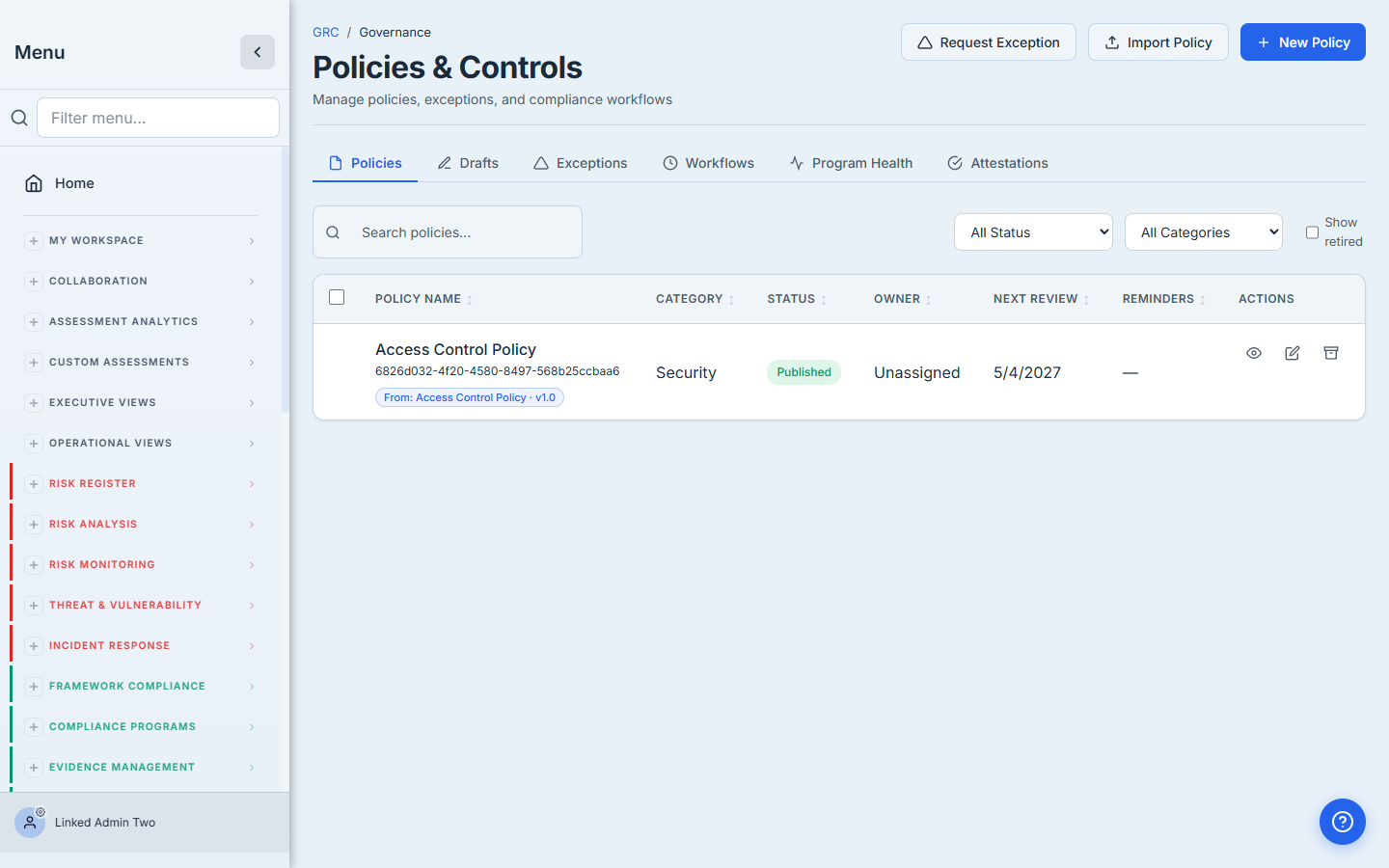
Step 1 — Click ”+ Import Policy”
Open /app/grc/governance and click + Import Policy in the header. The same screen also surfaces + New Policy — that’s the author from a template path. Use Import when you already have a finalized PDF or DOCX you want to bring under management.
Step 2 — Fill the import form
The form gives you everything an audit needs in one screen:
- File — PDF, DOCX, or any readable format. Talarity stores it in GCS and computes a SHA-256 fingerprint so you don’t accidentally double-upload the same document.
- Title and Version — what shows up in lists, searches, and reports.
- Category — picks the canonical 8-value taxonomy (Security, Privacy, Access, Incident, BC/DR, Vendor, HR, General). Same taxonomy used for KPI rollups.
- Effective Date — the date the policy takes effect.
- Next Review / Expiration — the date that drives every reminder downstream. Set it now. You can change it later, but every reminder cadence anchors to this field.
- Owner — the person on the hook for keeping this policy current. Reminders go to this user. Defaults to you, but pick the right owner if it isn’t.
- Description — what the policy covers. Free-form, but write something — the auditor reads this column first.
- Requires user attestation + Cadence — if your team needs every employee to acknowledge the policy on a cadence (annual, semi-annual, quarterly, monthly, or on-change), flip the toggle and pick the cadence.
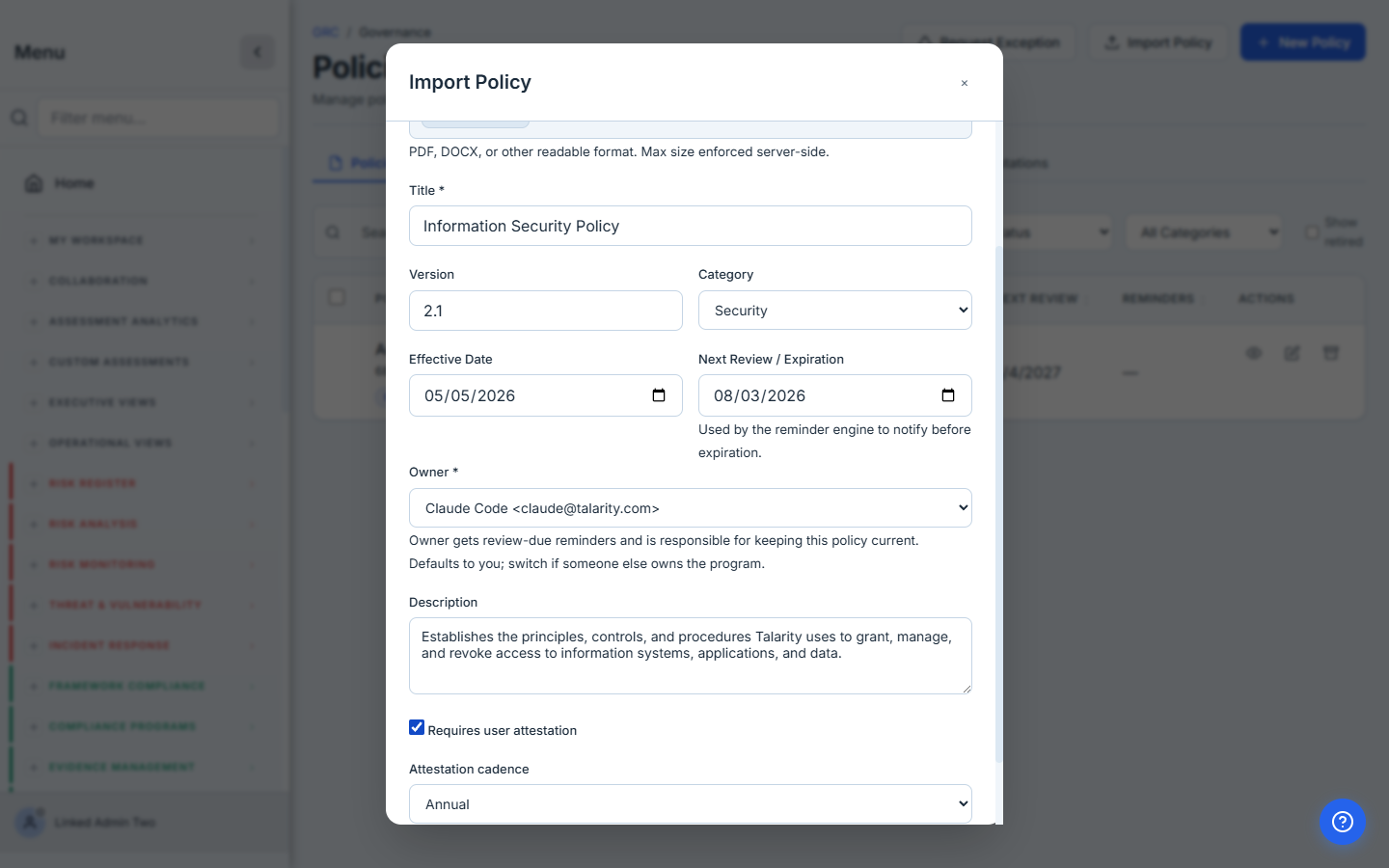
The owner picker is the most under-used field in this form. Most teams default it to themselves and forget. Three months later the reminder fires to the wrong inbox. Pick the right owner — the person who will actually update this policy when it next changes.
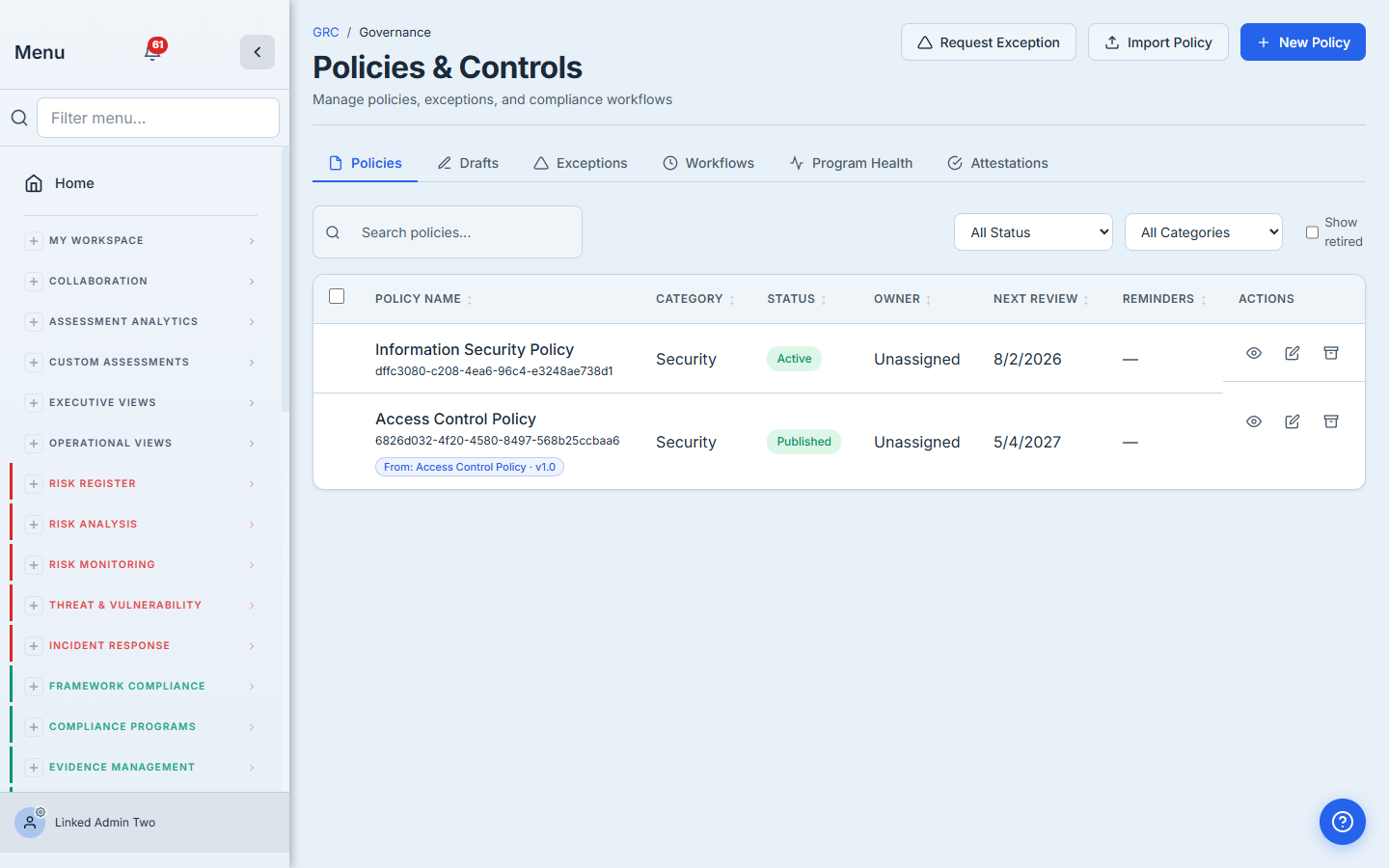
Step 3 — Submit. The policy lands in two places at once.
Click Import. If Talarity finds an identical file already in your Artifact Repository (same SHA-256), you get a “Link to Existing Artifact?” prompt — pick Link As-Is and the policy registers against the existing artifact instead of duplicating the upload. Otherwise the file uploads, the artifact is created, and the policy registers in one atomic write.
Behind the scenes Talarity:
- Stores the file in your Artifact Repository (
/app/artifact-repository) withdocumentType: 'policy-doc'. - Creates a policies row in the Policies tab with
status: 'active', the owner you picked, the review date, the attestation cadence, and a tracker link to the artifact. - Writes an
entity_linksrow with(source_kind=policy, source_id=policyId) ↔ (target_kind=artifact, target_id=artifactId, link_role=tracker). That tracker row is the canonical join — read by reminder logic, audit reports, and the cross-link affordance described below. - Logs a
policy.importedaudit event with the importer, the title, the artifact id, and the chosen owner.
Step 4 — Find the policy in the Policies tab
The policy appears immediately under Policies & Controls as Active. Category, owner, next review date, and reminder status are all surfaced in the table. Click the row to open the policy detail.
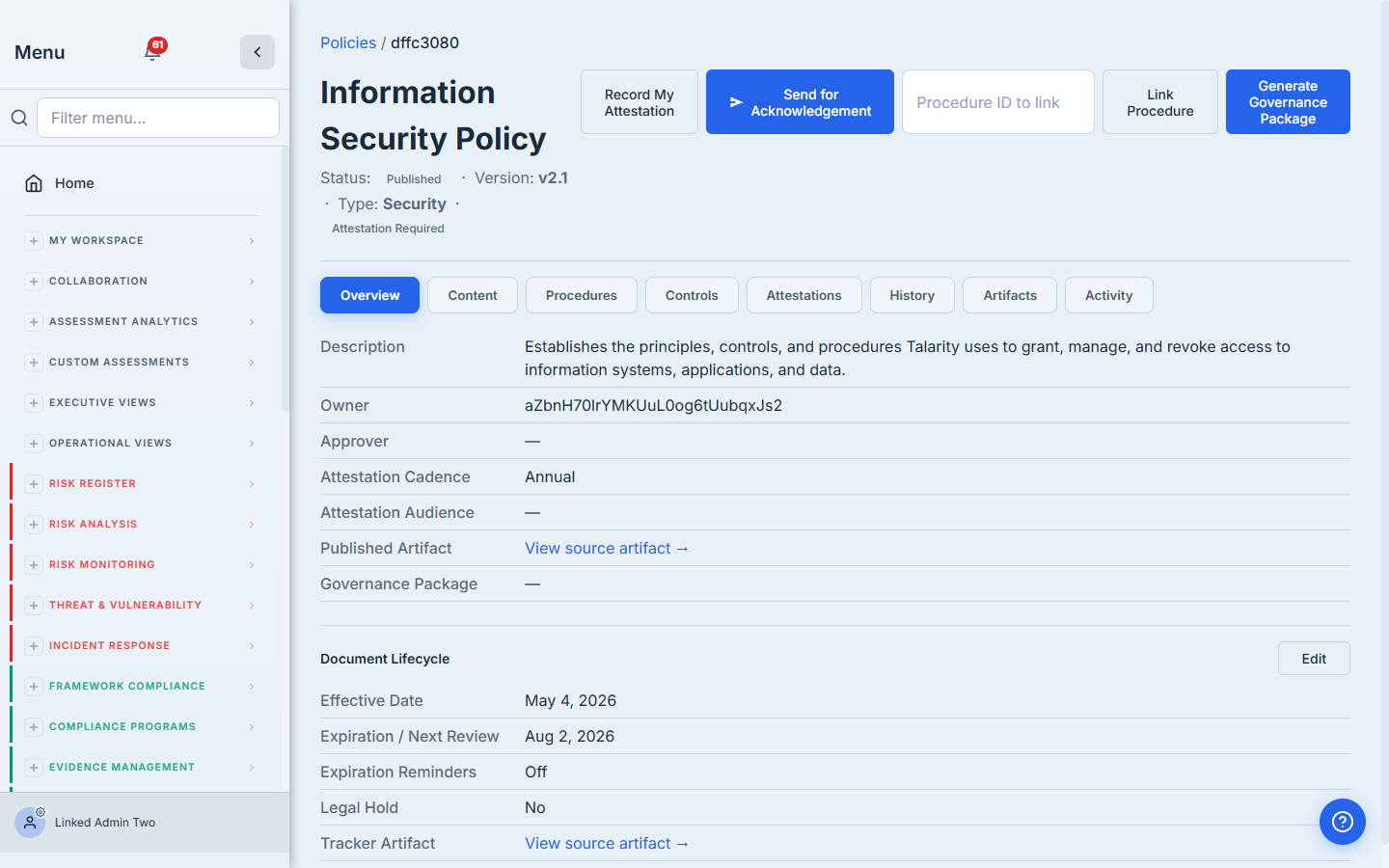
Look closely at the Overview metadata block. Two new affordances:
- Published Artifact → “View source artifact” — deep-link to the artifact in the Artifact Repository. Useful when an auditor asks “where’s the source file.”
- Tracker Artifact → “View source artifact” — second link in the Document Lifecycle section. Same destination; surfaced in two places because users approach the cross-link from both metadata blocks.
Step 5 — Click through to the Artifact Repository
Click either “View source artifact →” link. Talarity opens /app/artifact-repository on the All Artifacts tab, scrolls to the artifact, and pulses the row briefly so you don’t lose it in the list.
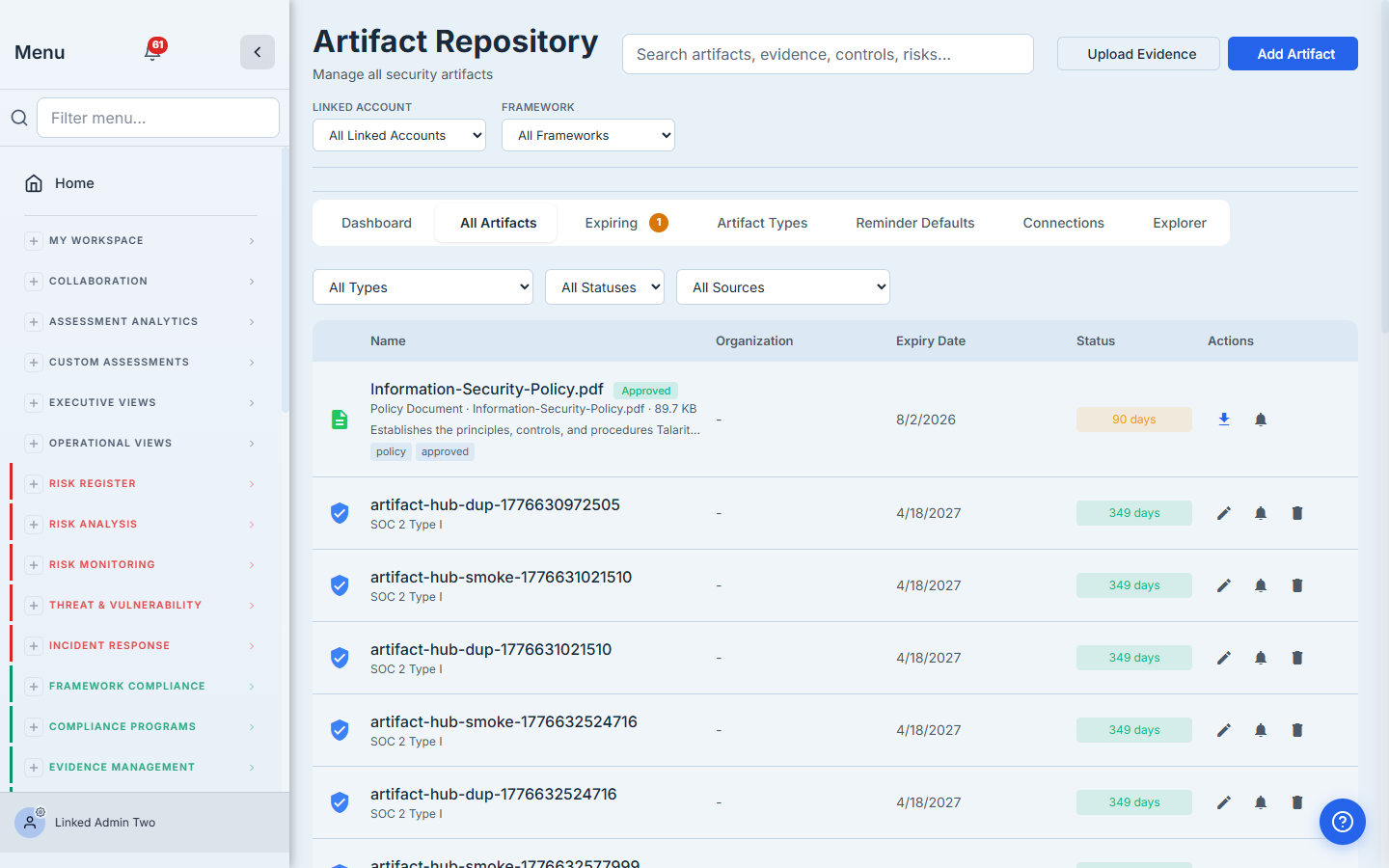
This is the cross-link in action. The same physical document is reachable from the Policies tab (where compliance leads live) and the Artifact Repository (where auditors and evidence collectors live). They’re two views of one thing — joined by the tracker link, not duplicated.
Step 6 — Configure review reminders
On the artifact row, click the bell icon to open Configure reminders. Here’s where the policy program goes from “we have this somewhere” to “we’ll never miss a review.”
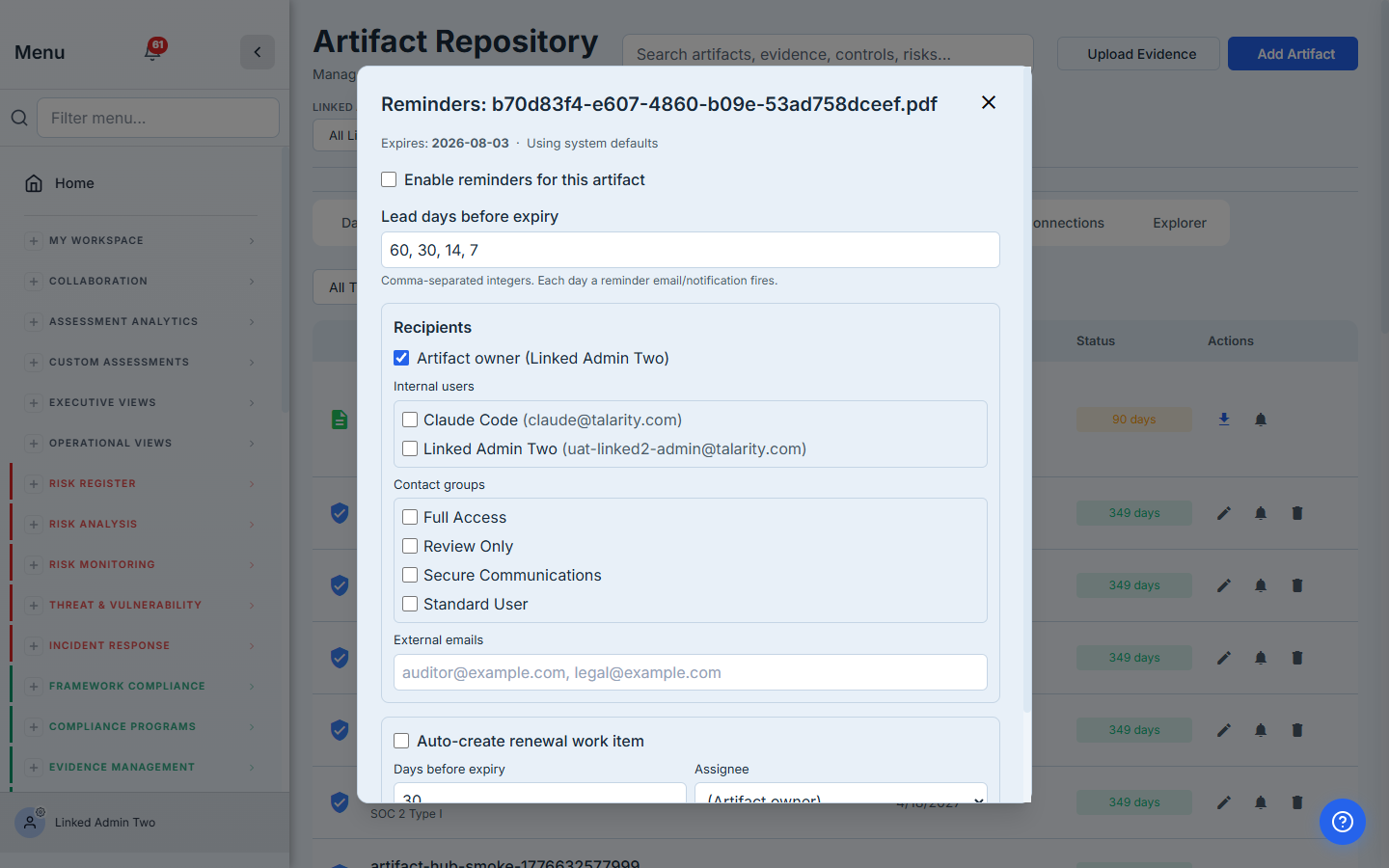
The defaults are good for most policies:
- Lead days before expiry: 60, 30, 14, 7. Talarity fires a notification at each tier. If you don’t want the early heads-up, drop the 60 — the others stay.
- Recipients: the artifact owner is checked by default. You can also notify specific internal users, entire contact groups (Full Access, Standard User, Review Only, etc.), or external auditor emails. The owner gets the email + in-app notification at every tier.
- Auto-create renewal work item. If you want a real task spawned in
/app/tasksN days before expiry — assigned to the owner with the original artifact attached — flip this on. The owner sees it in their My Work queue, can’t forget it, can’t claim “no one told me.”
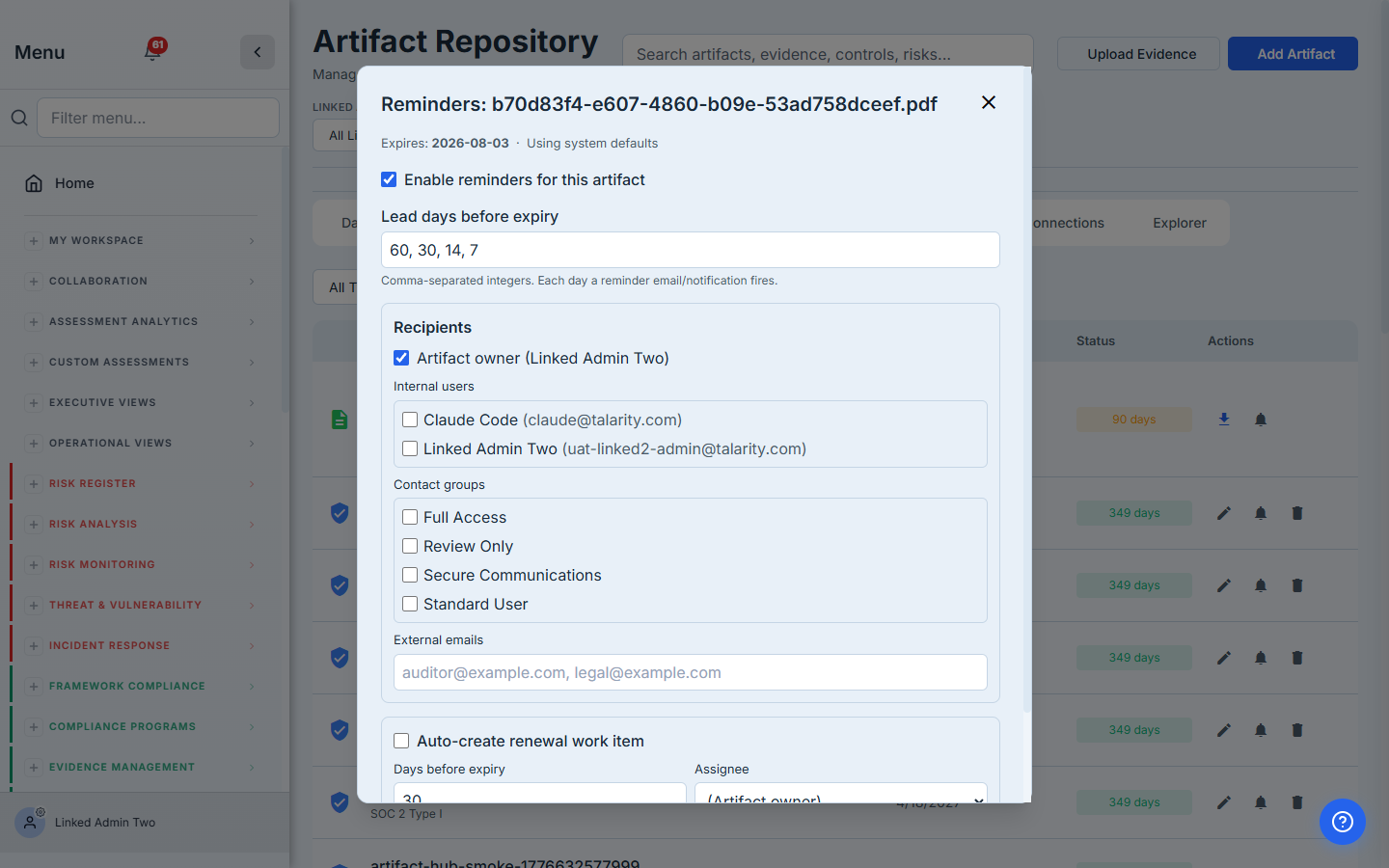
The bell icon on the artifact row turns blue once reminders are active. Audit-side: the reminder dispatcher logs every fire to policies.metadata.remindersSent with the tier and the timestamp, so an auditor reading the report can confirm the cadence actually ran.
Step 7 — Set defaults so you don’t have to do this 50 times
If your org has more than a handful of policies, configure once at the artifact-type level and let new uploads inherit. Open Reminder Defaults on the Artifact Repository:
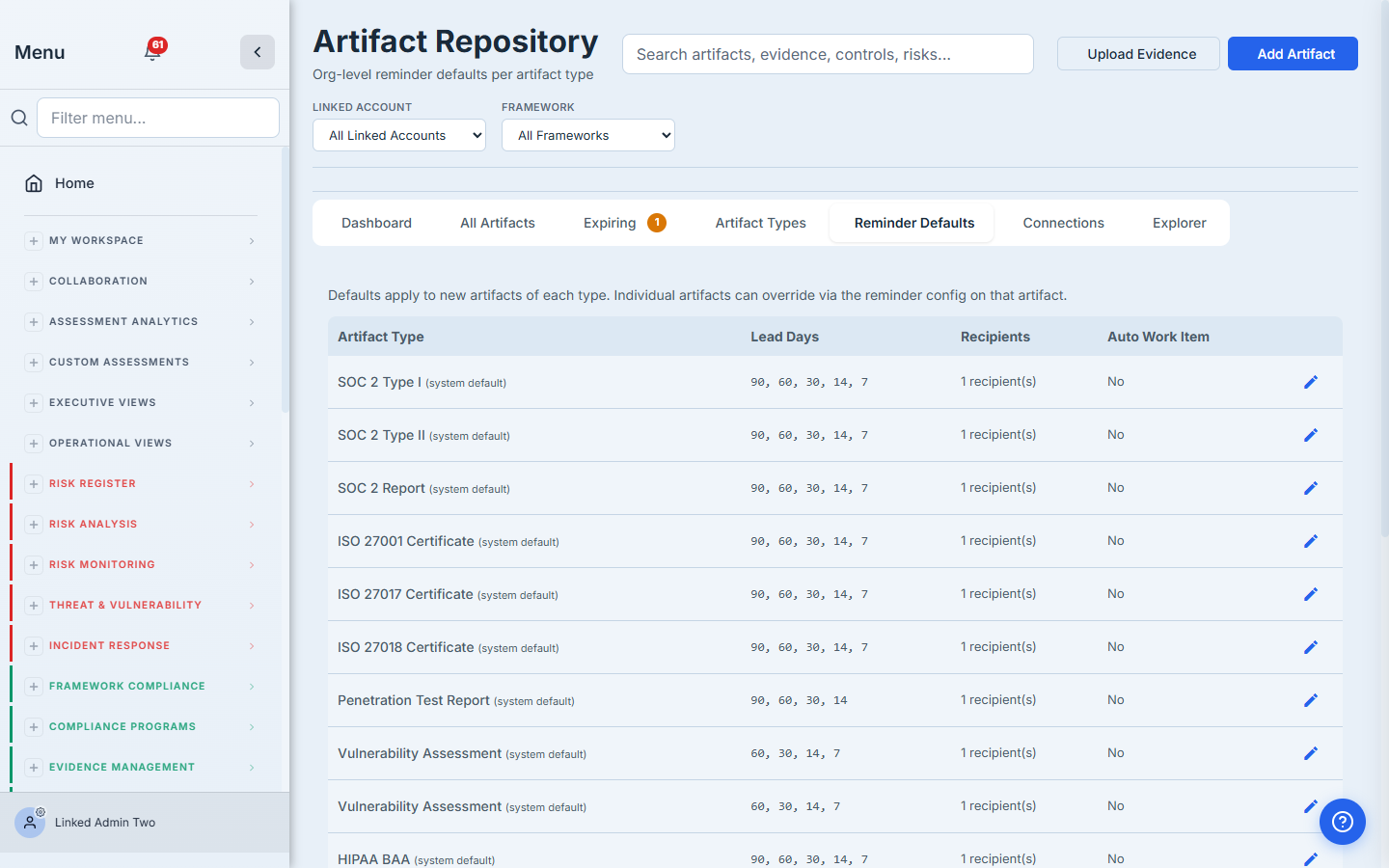
Edit the row for Policy Document once: set the lead days, the default recipients, the auto-renewal-work-item behavior. Every future policy import inherits them automatically. Individual artifacts can override on a case-by-case basis (Step 6 still works).
Step 8 — Track expirations program-wide
The Expiring tab gives you a single screen for “what’s due in the next 90 days”:
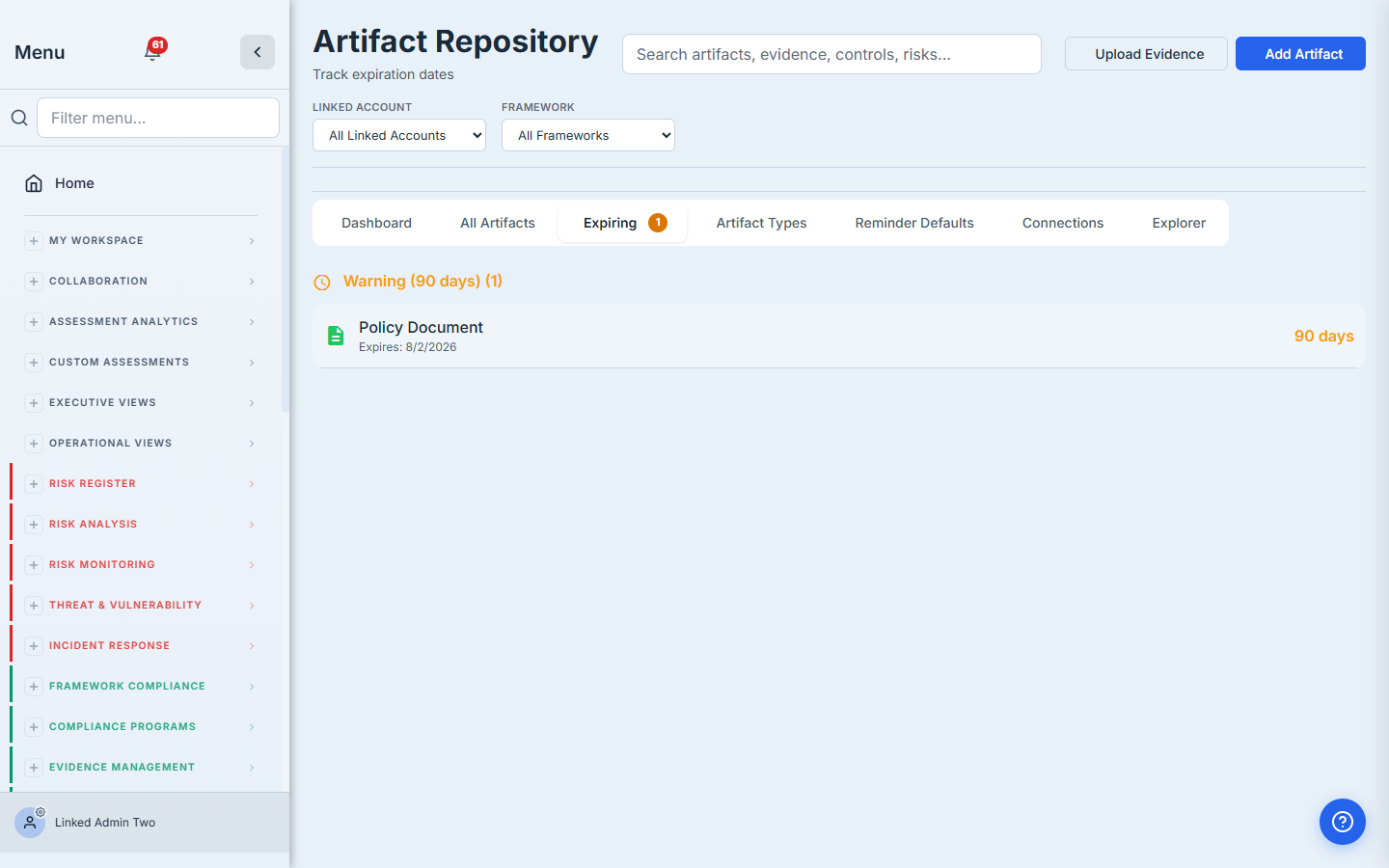
Bucket logic:
- Critical / Expired — 0 days or already past expiry. Auditors care.
- Warning — within 90 days. Owners should be acting.
- Valid — beyond 90 days, in policy.
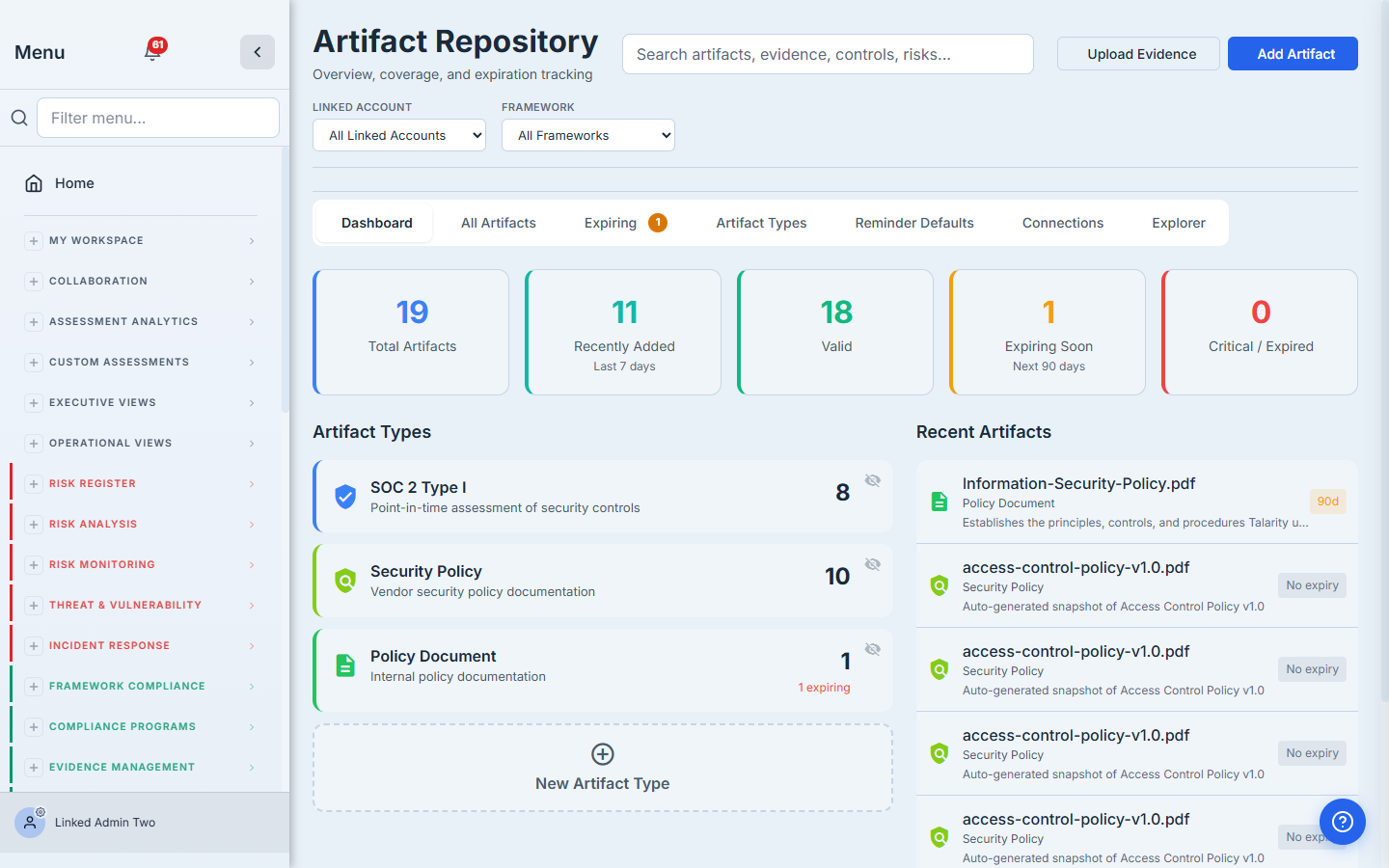
The Dashboard tab gives you the same data as KPIs: total artifacts, recently added, valid, expiring soon, critical/expired. Trend over time, not just point-in-time.
Step 9 — Audit trail on every policy
Open the Activity tab on the policy detail. Every state-change event lands here: created, owner change, attestation drive fired, review reminder dispatched, version bumped.
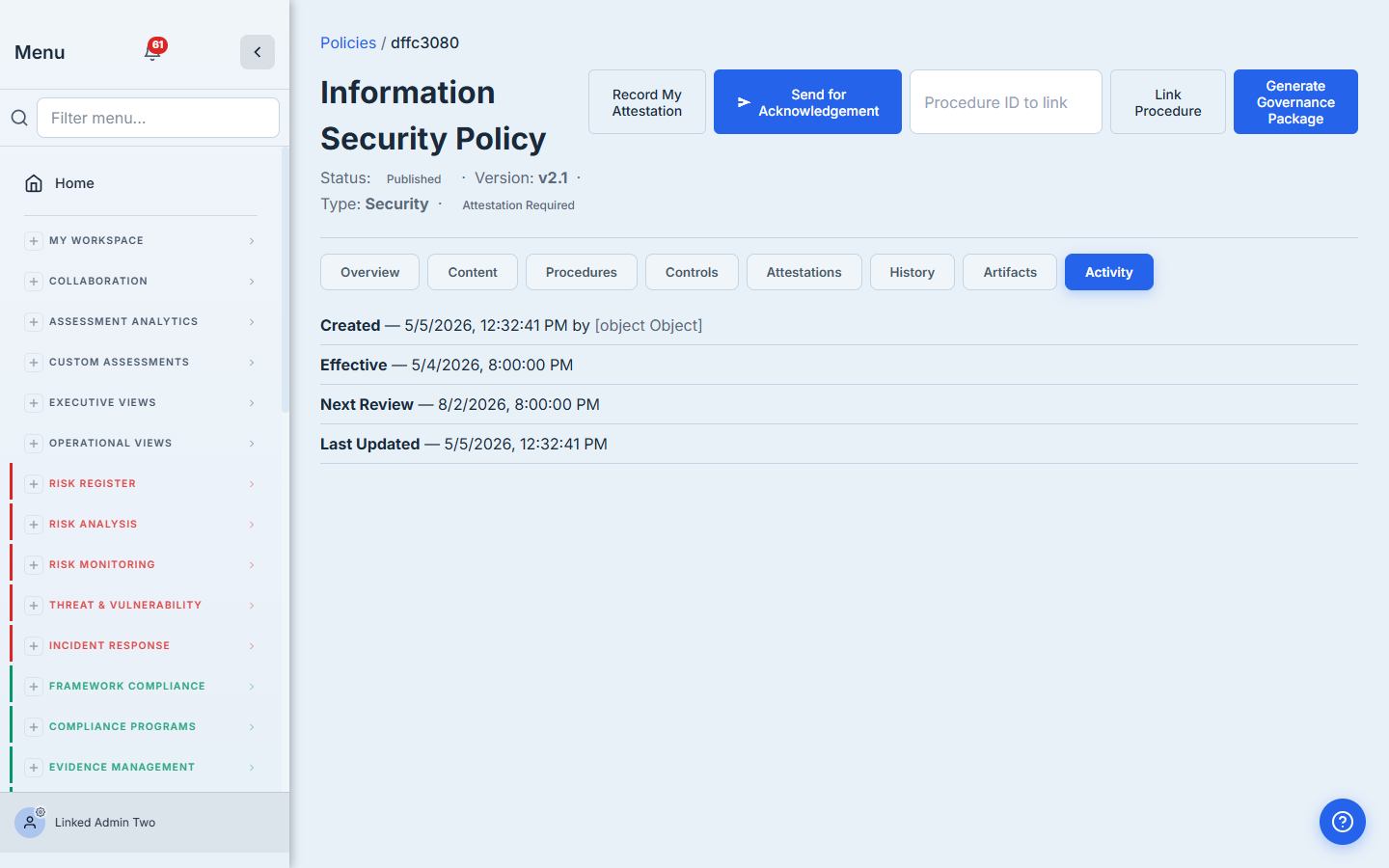
The History tab tracks predecessor / successor versions when you re-upload — so when v2.0 supersedes v1.0, the trail says so explicitly. Auditors love this because the report later says “v2.0 was reviewed on 2026-08-02 by Claude Code, replacing v1.0 which was effective 2025-04-15 to 2026-05-04,” and they can click straight through to either version.
What you walk away with
- One uploaded policy stored in two places — the Policies tab (program view) and the Artifact Repository (evidence view) — joined by an immutable tracker link, never duplicated.
- One owner picked at upload time, on the hook for review reminders that fire 60 / 30 / 14 / 7 days before expiry.
- One default reminder cadence per artifact type so future uploads inherit without manual setup.
- Optional auto-create renewal work item so the owner can’t forget — a real task lands in their queue with the artifact attached.
- A full audit trail on every policy: who imported, who owns, when reviews ran, when reminders fired.
Run yours this afternoon. Open /app/grc/governance, hit + Import Policy, drag in your Information Security Policy PDF. The first one takes about three minutes. Every renewal cycle after that — Talarity keeps the cadence so you don’t have to.